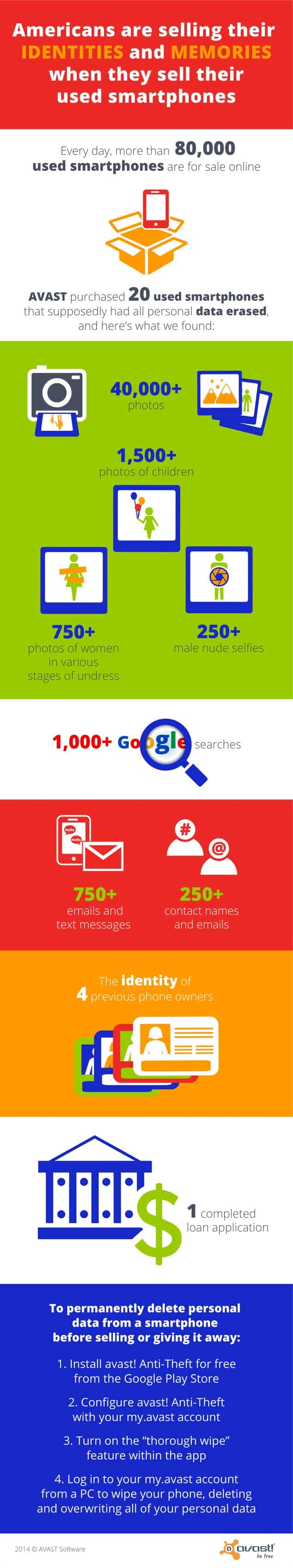
Most people use their phone for a while and then sell it, just because they want to go for the latest one, and this is most common in case of two kinds of people- gadget freaks and too rich people, who can’t use their smartphone for even a few months. Most people wipe their data and factory reset it, before selling it, thinking that all their data has been erased.
Recently, Avast experts bought 20 Android smartphones from eBay, among which there were two types- rooted and non-rooted phones. The phones were completely clean, but when they used some digital forensic tools to go deeper into the phones, they found many things, from selfies to porn, financial data to private messages.
Avast reported that none of those phones seemed to be completely clean. In the 20 phones, the researchers collected 40,000 locally stored photos, including more than 1,500 photos of children, more than 750 photos of partially or entirely nude women and more than 250 photos of partially or entirely nude men. They also revealed that they found out more than 1,000 Google search queries, more than 750 emails and text messages, more than 250 contact names and email addresses, and also one completed loan application.
And the most important part, one among those twenty phones had a security app installed, and from all the data they have found they can easily track down the original owner of the phone. Now if you’re an iPhone user, then the part is pretty easy because it has built-in hardware encryption, and you can just hit ‘Erase all content and settings’ but if you are an Android users you must encrypt it manually and then perform the factory reset. There are also third-party apps for Android which lets you encrypt your device. Avast also has such a solution, their Anti-theft app lets you do so, there are also some others like Lookout, Kaspersky, etc.